Cyber Security Audits
We perform security audits within your knowledge and control to detect security vulnerabilities against the attacks to information infrastructure of your company.
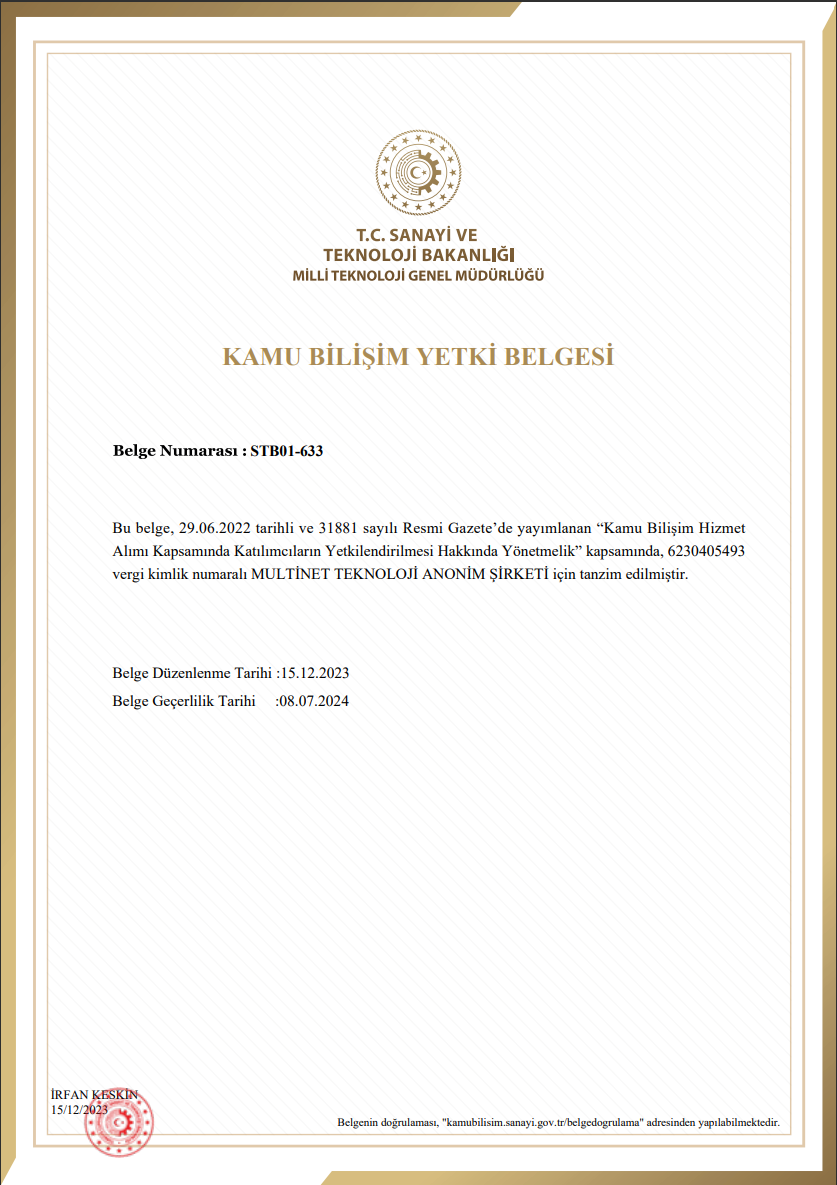
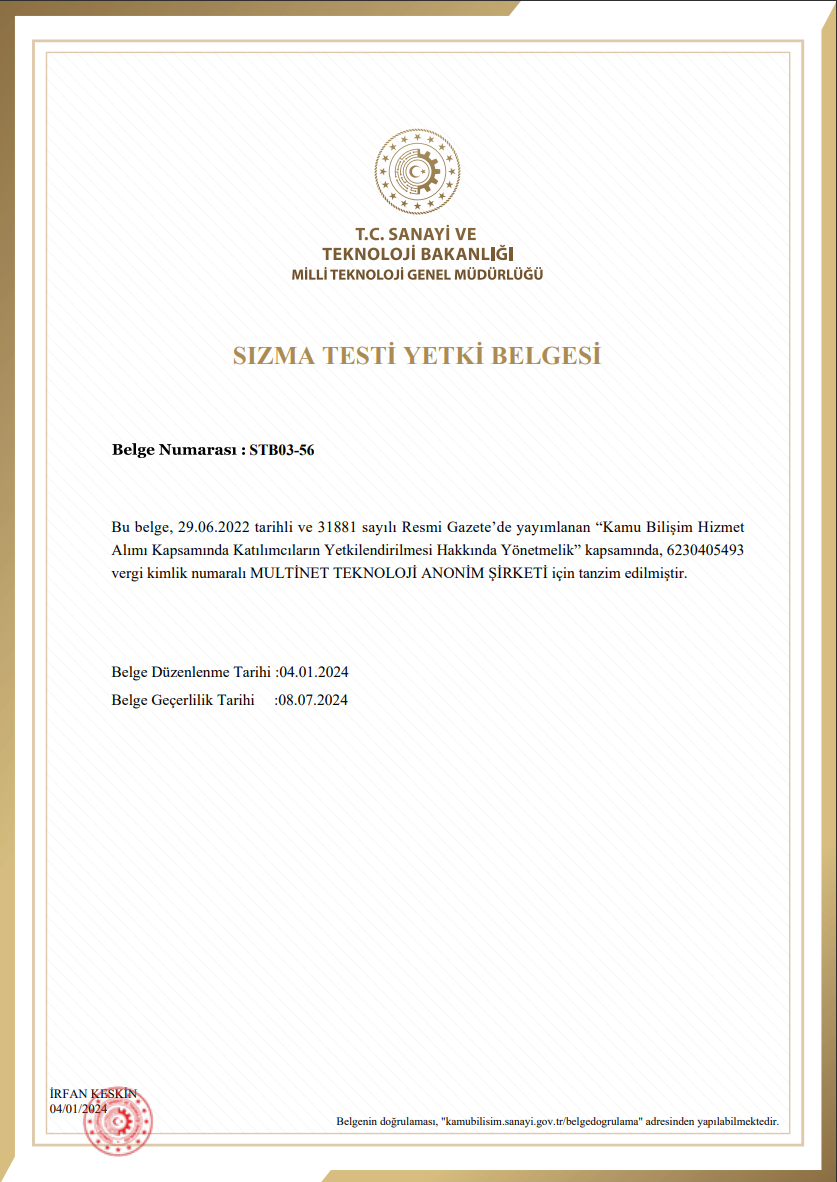
CERTİFİCATES
We Are a TSE Approved Penetration Test Firm
Securvent penetraiton team have the certifications; OSCP, ECSA, LPT, CEH applicable in the international area. Our services are performed by our personnels who has the certifications.
As Multinet Teknoloji A.Ş (inventiv, with the document no of TSE-STF-031, we are a TSE approved penetration test firm..
To get information about TSE approval, you can use the link below

Why Penetration Tests are Necesarry?
Sustainability
IT infrastracture is the lifeblood of a corporation and when it is not under control, can bring workflows to a standstill.
Data and Reputation Loss Risk
In any attack to your information systems, your sensitive data may get lost and your brand reputation may be damaged. Therefore you should make sure your sensitive data is always safe.
Regulative Obligations
If you have the certifications like TSE-Trust Stamp, KVKK, PCI-DSS, ISO27001 or you want to obtain, you should your IT systems get tested periodically by an authorized corporation and report.
What do you get with the penetration test service?
We report all vulnerabities we detected via the penetration test with a file specified for you and hand it to you. In The Penetration Test Report;
- Performed tests are controlled to validate, serious vulnerabilities are reported,
- All tests are grouped as «Critical, High, Medium, Low»,,
- Solution recommendations are offered for each detection.
![]()
SECURVENT
Articles About Cyber Security
SECURITY
Frequently Asked Questions
During a penetration test, high-qualified cyber security specialists take on an attacker role and try to break into a companies network. Like an attacker does, it reconnoitres on the network and exploits the security vulnerabilities to find an infirmity. This tests indicates to infirmities that can be exploited by a real hacker and offers a road map for improvement.
It differentiates depends on your companies operation field and “attacker attractiveness”. It is recommended that for companies engaged in highly sensitive operations pentests should be performed a few times in a year in order. The purpose is to test the latest attacking way. For the companies which engaged in less sensitive operations, it is recommended that pentests should be performed subsequently a new version or major feature updates.
inventiv offers you an explicit audit report which indicates; what and how have been tested, which vulnerabilities it has and how to use them. The report includes; screenshots, stolen data summaries and scenarios for re-attacks.
As inventiv, during a penetration test, we don’t share any secret information we would encounter, to a place except yours. The elements we found, only specifies as Anonymous to explain a security vulnerability in the audit report. In addition, the audit reports are kept only for a limited time by inventiv.
Goals of a penetration test, differentiates tremendously according to the scope it examines. In general, the purpose of a penetration test is to verify the effectiveness of controls designed to secure the preserved system or assets.
Penetration test always should report the projects goals. Penetration test reports, should summerize the scope, requirements and results.
Since security infirmity scans, use recognition features that were configured in advance, a system has points that can’t be tested completely. Penetration test, provides a range for serious security errors that browsers wouldn’t be able to test and it absolutely increases the companies security standing.
Our metodology of penetration test, has been specially designed for removing data loss, downtime and risks. When taking advantage of a security weakness carries a risk for the system, we will documentate the security weakness and report it for our customers. We will not engage in any activity that will disrupt your systems.
A succesful penetration test is deemed as start point to give priority to indisputable proof of the problem and to fix. Penetration test, focuses on high concentrated security vulnerabilities and removes falses and positives.
Time of the penetration test depends on the type of the systems and the amount with the test. In normal conditions a test time takes 1-2 weeks.
